A cyber espionage campaign, attributed to a China-based group, has been targeting military organizations in Southeast Asia since at least 2020. Identified by Palo Alto Networks' Unit 42 as CL-STA-1087, the operation is characterized by its methodical approach to intelligence gathering rather than mass data theft.
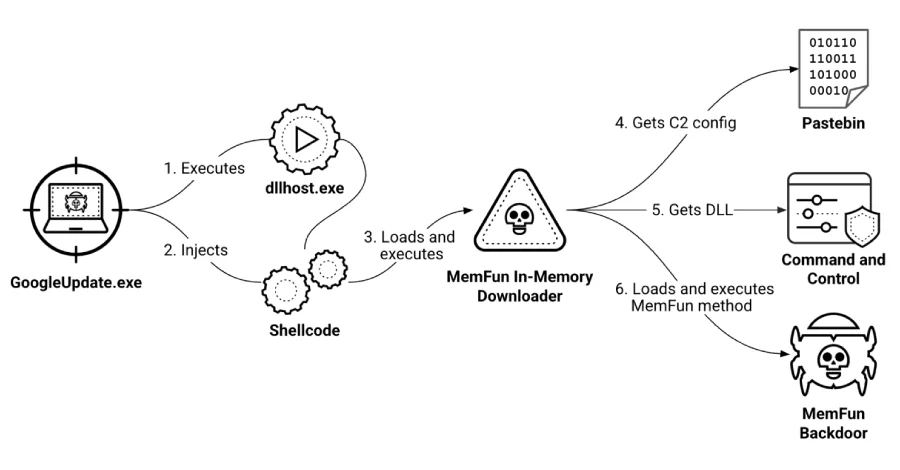
The attackers have focused on collecting sensitive information, particularly concerning military capabilities and collaboration with Western forces. This operation employs advanced persistent threat (APT) techniques, utilizing backdoors named AppleChris and MemFun, along with a credential harvester called Getpass. Researchers noted that the attackers demonstrated strategic patience, employing sophisticated methods to maintain access to compromised systems.
Malicious activity was uncovered following the detection of unusual PowerShell executions that allowed the attackers to establish a connection to a command-and-control (C2) server. The precise method of initial access is still unclear, but the deployment of AppleChris across various endpoints suggests a deliberate strategy aimed at evading detection and ensuring operational persistence.