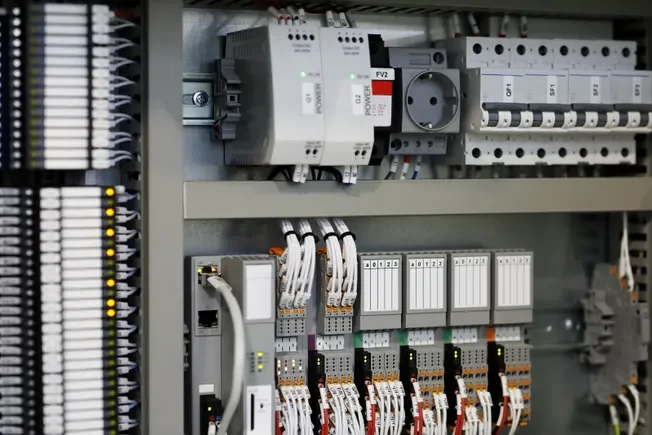
Over 5,000 industrial control devices are at risk globally due to Iranian hackers targeting critical infrastructure, with approximately 3,900 located in the United States. A new report by Censys highlights that U.S. government agencies have raised alarms over attempts to compromise infrastructure operators using vulnerabilities in Rockwell Automation's Allen-Bradley programmable logic controllers (PLCs).
According to Censys, the United States holds a staggering 74.6% of the global exposure to these devices, reflecting Rockwell's significant market share in North American industrial automation. Many of these PLCs are connected via cellular modems, indicating their deployment in remote areas, thus creating a vulnerable infrastructure network.
Recent activities by Iran-affiliated hackers have intensified, particularly in the wake of conflicts involving the U.S. and Israel. Some PLCs are also linked through Starlink satellite terminals, complicating monitoring and updates. Censys warns that numerous devices are accessible through standard services like HTTP and VNC, which broadens the attack surface and poses serious risks to operational integrity.