From June to December 2025, malicious actors exploited vulnerabilities in older versions of Notepad++ by serving counterfeit updates from the official site. This breach allowed the installation of malware due to inadequate verification mechanisms in the app, affecting targeted users who unknowingly downloaded a compromised version.
The attack was traced back to external sources, with researchers suggesting involvement from a Chinese state-sponsored group. As the Notepad++ team continues to investigate the incident, they confirmed that it originated from their hosting service at notepad-plus-plus.org.
The malicious agents manipulated the update process, redirecting requests from specific users to a harmful update manifest. This approach not only compromised their systems but also potentially enabled remote access to their keyboards, indicating a more sophisticated motive beyond mere data theft.
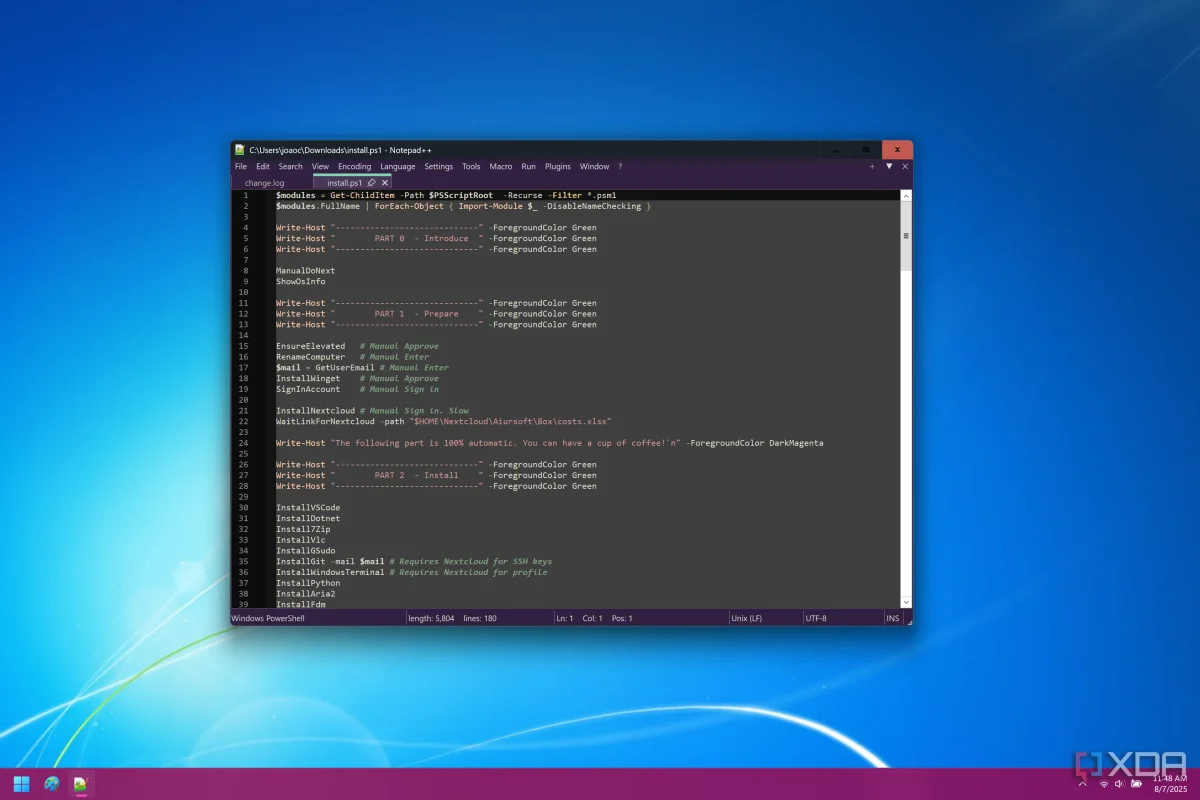
Despite the alarming nature of the attack, the Notepad++ developers were not responsible for the breach, and the app remains a widely trusted alternative for Windows power-users.